Security Measures Webinar Replay
March 19, 2025
How Will Your Security Measures and Incident Response Plan Hold Up During an Attack?
How Will Your Security Measures and Incident Response Plan Hold Up During an Attack?
Cyber threats are evolving rapidly, and businesses must stay proactive in strengthening their security measures and incident response plans. At our recent event, industry experts shared their insights on common pitfalls, best practices, and actionable steps businesses should take to fortify their cybersecurity defenses:
• Paul Love, Owner & Founder of CyberTron
• Chris Snipes, Senior Systems Engineer at CyberCore Technologies
• Carl Drago, Owner of Cyber-Construction, Inc.
The Most Common Cybersecurity Threats
One of the key discussions during the event revolved around the top threats businesses face today. According to a survey of over 300 technical decision-makers:
• 48% identified phishing attacks as their biggest security concern.
• 37% pointed to malware and ransomware.
• 35% cited user error as a critical risk factor.
• 31% noted data breaches as a significant threat.
(Source: Event discussion at 4:00 timestamp)
As panelist Chris Snipes highlighted, phishing and user error often go hand in hand, making employee training one of the most effective preventive measures. Carl Drago added that while security solutions are improving daily, cybercriminals constantly adapt, making ongoing vigilance essential.
Key Areas for Technological Improvements
When asked which areas businesses plan to improve in terms of technology, survey respondents provided valuable insights (see Figure 1 below):
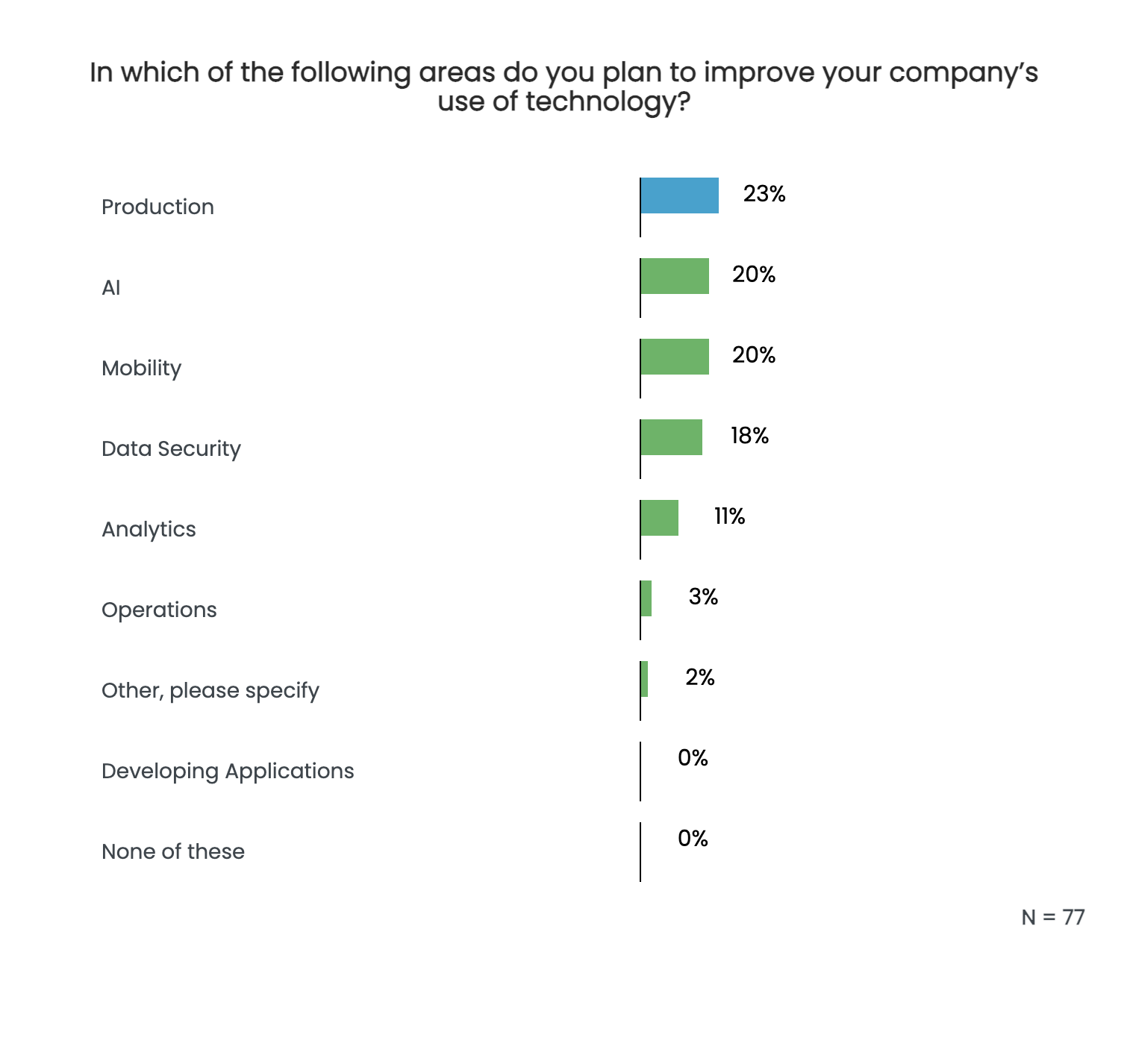
• 23% of respondents plan to improve technology in production.
• 20% aim to enhance AI capabilities.
• 20% are focusing on mobility, while 18% prioritize data security.
Chris emphasized the importance of multi-factor authentication (MFA) as a first-line defense, urging organizations that lack MFA implementation to make it a top priority.
Business Technology Objectives for the Next 12 Months
Survey results also revealed companies' primary technology objectives for the coming year (see Figure 2 below):
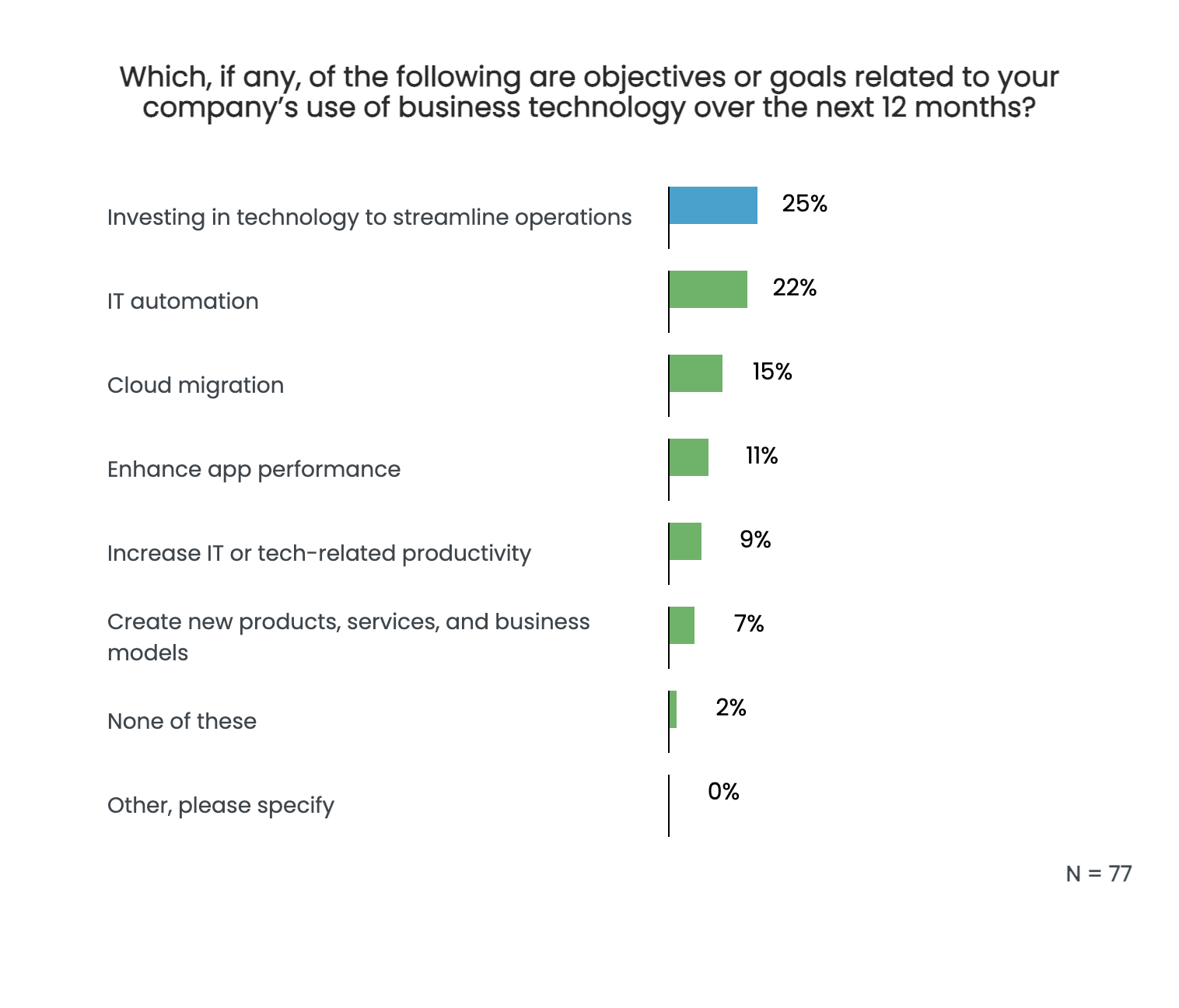
• 25% are investing in technology to streamline operations.
• 22% prioritize IT automation.
• 15% are focused on cloud migration.
Panelists stressed that while automation and cloud migration improve efficiency, businesses must also prioritize cyber resilience to ensure these advancements do not introduce new vulnerabilities.
How to Strengthen Your Incident Response Plan
A significant gap in cybersecurity readiness is the lack of sufficient incident response planning.
Survey results showed that:
• 65% of companies claim to have a business continuity or disaster recovery plan.
• 25% do not have any formal plan in place.
• 10% are unsure whether they have one at all.
Carl Drago noted that many businesses overestimate the effectiveness of their existing plans, often realizing too late that their backup solutions are outdated. He urged businesses to conduct regular security assessments and penetration testing to identify weaknesses before a cyberattack exposes them.
Top Security Priorities for Small Businesses
For small businesses with limited budgets, our panelists agreed on several must-have security measures:
• Email Security & Filtering – Investing in strong phishing filters prevents most threats before they reach employees.
• Employee Security Training – Educating staff on social engineering tactics and phishing scams reduces human error-related breaches.
• Multi-Factor Authentication (MFA) – Enabling MFA on all accounts significantly lowers the risk of unauthorized access.
• Endpoint Protection – Protects company devices from malware, ransomware, and other cyber threats. Many modern endpoint security solutions offer a combination of antivirus, firewall, and threat detection in one package.
• Vulnerability Scanning & Penetration Testing – Regular security assessments help businesses identify weak points before hackers exploit them. Chris emphasized the need for continuous security reviews to ensure businesses stay protected.
As Paul Love pointed out, many security solutions are more affordable than businesses realize and can be implemented at little to no cost, such as enabling MFA on existing accounts.
Final Thoughts
The evolving threat landscape means businesses must continuously evaluate and update their security strategies. Whether it’s training employees, implementing multi-factor authentication, or investing in endpoint protection, taking proactive steps now can prevent costly breaches in the future.
Want to learn more? Watch the full event replay and access additional resources on how to enhance your cybersecurity strategy today!



 Join Our Insight Rewards Network
Join Our Insight Rewards Network